Introduction
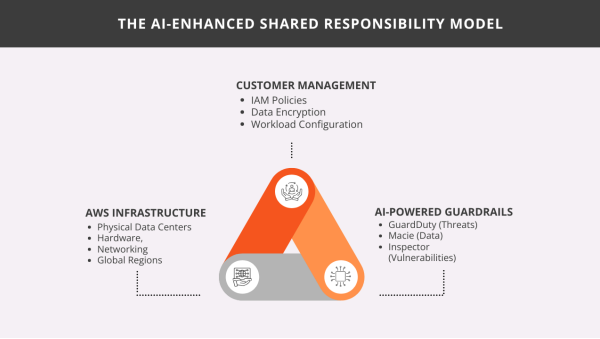
The shift in the global threat landscape in 2026 has rendered traditional, rule-based security perimeters insufficient. As organizations navigate an environment where Agentic AI threats can identify and exploit misconfigurations in sub-second intervals, the “reactive” security model is no longer a viable defense strategy. This new reality necessitates a transition toward Predictive Resilience. By integrating Machine Learning (ML) directly into the fabric of aws web services, security has moved from static rule matching to behavioral baseline analysis. At Xammer, we have observed that the most resilient enterprises are those that eliminate “response lag” by shifting decision-making from human-in-the-loop approvals to automated, silicon-level defenses powered by our specialized AI-native frameworks.
The AWS AI Security Ecosystem: A Unified Intelligence Fabric
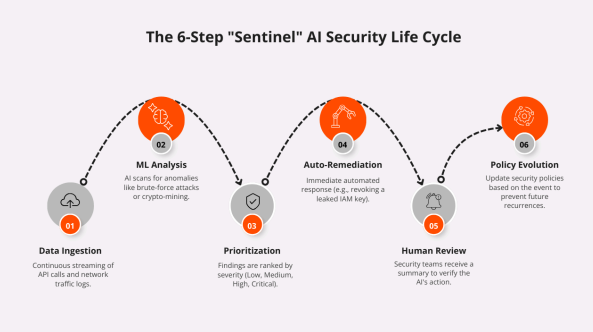
The modern AWS cloud computing security ecosystem is no longer a collection of isolated tools but a unified, autonomous fabric. This infrastructure operates as a continuous, closed-loop system, shifting the burden of defense from manual triage to algorithmic precision through the 6-Phase Sentinel Life Cycle.
● Phase 1: Data Ingestion: The cycle begins by streaming raw telemetry into the Amazon Security Lake. By normalizing logs from CloudTrail and VPC Flow Logs, the fabric creates a single, high-fidelity data source for your cloud it infrastructure.
● Phase 2: ML Analysis: Amazon GuardDuty and Amazon Inspector perform deep machine learning analysis to establish behavioral baselines for every user and resource.
● Phase 3: Prioritization: AWS Security Hub acts as the central risk engine. By leveraging Automated Reasoning, the system ranks findings by actual environmental severity, ensuring focus on the critical 2% of risks.
● Phase 4: Auto-Remediation: The fabric triggers automated playbooks via AWS Systems Manager. For instance, if Amazon Macie discovers exposed sensitive data, the system revokes public access in milliseconds.
● Phase 5: Human Review: The system provides an AI-generated narrative of the event, ensuring that security remains a transparent business process.
● Phase 6: Policy Evolution: Insights are fed back into the Governance layer to automatically refine IAM policies and security groups.
Implementation Strategy 1: Autonomous Threat Detection
Modern threat detection requires moving beyond simple anomaly identification. By utilizing aws cloud technologies, organizations can implement a system that monitors activity across VPC Flow Logs and EKS runtime environments simultaneously.
In this paradigm, detection leverages ML-driven Signal Correlation to identify “Attack Kill-Chains.” For instance, cross-referencing an unusual API call in Bedrock with a latent credential exfiltration attempt on an EC2 instance provides high-confidence alerts on sophisticated threats before an attacker can achieve persistence.
Implementation Strategy 2: Data Privacy through Intelligent Discovery
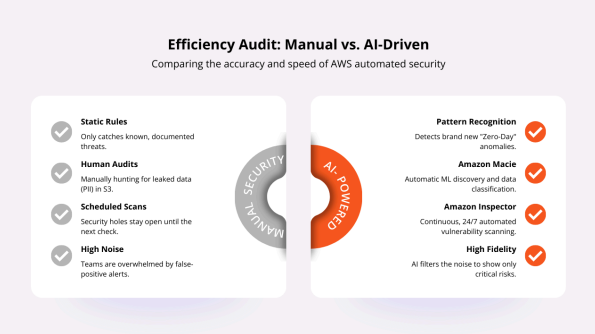
As data becomes the core propellant for enterprise AI, its protection requires more than just encryption. Amazon cloud based services like Amazon Macie use Natural Language Processing (NLP) to automate the discovery of Personally Identifiable Information (PII) across petabyte-scale S3 environments.
This automated “Data Guardian” distinguishes between public documents and sensitive RAG (Retrieval-Augmented Generation) datasets, triggering immediate remediation if proprietary training data is inadvertently exposed.
Implementation Strategy 3: Continuous Exposure Management
The traditional concept of a “vulnerability scan” has been replaced by Continuous Exposure Management. As the industry standardizes on Agentless Scanning across EC2 and Lambda, success depends on Predictive Risk Scoring within the infrastructure cloud computing layer.
Rather than prioritizing based on generic scores, the system analyzes whether a vulnerability is actually reachable via an internet-facing gateway. This allows cloud computing it services teams to focus exclusively on exploitable vulnerabilities, significantly reducing Mean Time to Remediation (MTTR).
Best Practices & Cost Optimization
Operationalizing an AI-powered security stack requires balancing depth of defense with cloud expenditure. To maintain optimized Security Economics, we recommend prioritizing these areas:
1. Consolidated Operations: Use Security Hub to unify findings, reducing the cost of multiple third-party cloud service providers and dashboard licenses.
2. Targeted Discovery: Use Macie’s targeted sampling to focus on high-churn buckets rather than scanning 100% of data repositories daily.
3. Automated Remediation: Implement AWS Systems Manager (SSM) playbooks to automatically isolate compromised assets. This prevents lateral movement, the most expensive component of a data breach.
Conclusion
The transition from rule-based to AI-powered security is the defining architectural shift of 2026. By moving beyond reactive monitoring toward Autonomous Security Governance, businesses can stay ahead of increasingly sophisticated adversaries. The integration of automated reasoning and intelligent threat detection creates a self-defending digital ecosystem.
At Xammer, we specialize in deploying these amazon web services in cloud computing strategies to ensure your infrastructure is not just compliant, but inherently resilient. By adopting a Xammer-led security posture, you are securing the future of your enterprise on a foundation of proactive, silicon-level intelligence.
FAQs
1. How does AI-powered security help eliminate "Alert Fatigue"?
AI systems use Signal Correlation to group hundreds of related events into a single, context-rich "Finding." This allows analysts to investigate a single narrative rather than being overwhelmed by disconnected alerts from various cloud based computing services.
2. What is the benefit of "Automated Reasoning" over traditional scanning?
Traditional scanning looks for known signatures. Automated Reasoning uses formal logic to mathematically prove that a configuration is secure, identifying "Zero-Day Misconfigurations" that traditional cloud computing technology filters miss.
3. Does Amazon Macie scan data within AI training pipelines?
Yes. Macie monitors S3 buckets feeding into Amazon Bedrock and SageMaker pipelines, ensuring sensitive internal data isn't accidentally included in datasets used to train public-facing models.
4. How has Amazon Inspector changed in 2026?
It has moved to Continuous Agentless Scanning across all type of cloud computing services, providing a Software Bill of Materials (SBOM) and contextual risk scoring based on actual network reachability.
5. Is AI-powered security significantly more expensive?
While there is an inference cost, it leads to a lower Total Cost of Security. By preventing expensive breaches through faster detection, most organizations see a positive ROI compared to manual methods offered by generic cloud computing service providers.

